The Internet has always been a mixed blessing for mankind. With online education, transactions, communications, etc on one side shining as boons and malware, phishing, scams, hacking, etc on the other side shadowing as a bane. There are many aspects of how you can protect yourself from the dangers of the internet and one of them relates to how to protect personal data online. Your personal information is your strength when it remains with you and at the same time becomes your major weakness when it is compromised.
Personal data is your property and it is a crime to interfere with someone’s privacy. More than social ethics, misuse of personal data can also lead to identity theft. Let us identify certain mistakes that we all do and know about the correct procedures when it comes to handling personal information.
Different Methods On How To Protect Personal Data
Here is a checklist of the important methods to be considered while handling personal information online.
Let Us Check Each Method In Detail –
1. Keep Your Devices Password Protected

Your devices contain more information about you than you can think of. It is important to keep this information safe and the first way of doing so is to keep your devices locked with a passcode, fingerprint impression, or pattern. God Forbid, but if you leave your phone, tablet, or laptop in a cab or café, or if it gets stolen in places overflowing with crowds like the market or stations. Life would be in a mess if the devices did not have a lock. A locked device is difficult to hack into and personal information is at a far lesser chance of being compromised.
2. Use Passwords That Are Difficult To Guess

The second point is an extension of the previous method and this involves creating passwords that are impossible to hack. In other words, just choose a strong and unique password making it impossible to guess and very difficult to crack. Most of us have the habit of keeping the same password for a number of our online accounts and emails which means if the password of any of our accounts is comprised, all our accounts can be easily hacked into. An example of a strong password would be the first letters of a phrase.
“I want to travel the Globe” becomes “Iw2ttG”
It is easy to create strong and unique passwords but the real challenge lies in remembering them. And keeping a list in your wallet or making a note of them in your diary is not the solution. For this, you need to use a password manager software that stores all your password for you while you have to remember just one that unlocks the Password manager app every time you need a password.

TweakPass is an amazing application that acts as a password vault and stores all your credentials for you. You can use this app on multiple devices with the same account which means that you can autofill the credentials on all your devices. For a better understanding of this product, read the complete review by click on the link below:
TweakPass: The Ultimate Password Manager
3. Limit Sharing On Social Media

When you share an image on social media, you do not realize that you have shared more than just the image. To understand that, first, you must know that any image clicked with a camera- DLSR, smartphone camera, or any other device with a lens, captures and stores a lot of information like geo-location, device name, date, and time of the photo clicked. This information known as Metadata has been used by people with malicious intent to track the location of others. However, if you do want to post your photos online on social media platforms, then you must follow these steps:
Step 1: Change Your Privacy Settings on Social Media apps and limit the number of people, you can view your photos and personal information.
Step 2: Erase all the Metadata from every image you share online with your friends and family. This will ensure that personal information is safe and will not fall into unrequired or unauthorized hands.

An important tool to completely wipe off your photos’ Exif information is Photo Exit Editor. This is an easy to use program that allows you to add, edit, or delete any sort of information stored within the image file. For more details, check the article given below:
4. Remain Extra Cautious When Using Free Wi-Fi

Free Wi-Fi is like a beach where there are people from several towns and cities gather to have a good time. This means that you can see what everyone is doing as there is nothing private or hidden. A public Wi-Fi is a similar virtual location where certain people with malicious intent try to eavesdrop on others and gather their personal information along with credentials. This is rarely possible when you are on your home or office network.
It is recommended not to do any sort of transaction or check your emails when on public Wi-Fi. I would not suggest that you ever join one. But if you have to then the best way to do is to use a VPN app on your device.
There are countless VPN services available on the global software market. But many people do not know what features you would want to avail yourself of after purchasing a VPN. For example, Masking your IP address while using public Wi-Fi is the basic functionality of a Virtual Private Network and should not be considered as an additional feature. I have been using Systweak VPN for almost a year now and here are some features that give it an edge over others:
Security and Privacy: All your internet activity is secured and private.
Breaks Regional Barriers: You can watch Netflix content blocked based on Geolocation.
Encrypted File Sharing: All the files sent and received over the internet are encrypted with military-grade encryption.
Secured Remote Access: You can take the secured remote access of your home or office computer sitting anywhere in the world and even using public Wi-Fi.
Gaming: Apart from the benefit of keeping your gaming credentials safe, you can now connect to different servers across the globe when playing multiplayer games.
Complete review on Systweak VPN
5. Deactivate Old And Unused Online Accounts
Another way of securing personal data is to identify unused accounts and emails created online and deactivate them permanently. This includes any accounts you might have created on eCommerce websites that you no longer use. Any account created online includes your name, phone, and email address along with your credentials. If any of these old and unattended accounts is compromised, then hackers can get a lot of personal information about you. The lesser information kept online, the more secure you are.
6. Two-Factor Authentication

A new method of protecting personal data is by implementing Two-Factor Authentication. This is double confirmation of signing into a new device or conducting an online transaction and is now provided by most banks and email providers. The following scenarios will help understand this concept in a better way.
Scenario 1: Sign-in to your Gmail account on a new device
When you enter your Gmail account credentials on a new device with the Two-Factor Authentication turned on, it will send a prompt on your Android device asking you to tap the Allow button. This way it confirms if the signing in to the new device is legit or not.
Scenario 2: OTP received for Online Transactions
When you try to make an online transaction through your Credit/Debit card, you always receive a One Time Password or OTP on your mobile without which the transaction will not proceed further. This feature is the bank’s way of authenticating whether the online transaction is authorized or not.
Note: Check if the Two-Factor authentication is turned on for your email and online transaction services. If not, then contact the support team to get this feature enabled at once. Once enabled, the Two-Factor Authentication process may seem a bit time & effort consuming each time you have to enter the OTP but the benefit of being safe is worth all that.
7. Install an Antivirus with Real-Time and Exploit Protection

There are some things that you cannot prevent just by changing the settings or staying cautious. And those are malware, spyware, adware, etc threats that try to access your system on a real-time basis when you are surfing the internet. To escape these attacks, you must have a powerful antivirus that offers real-time protection and prevent any malicious software from entering your system. Systweak Antivirus is one such application that facilitates blocking ads with its StopAll Ads extension and blocks the entry of trackers in your system at the initial level.
Speaking of Antivirus software, one of the best Antiviruses in the market is Systweak Antivirus which is a fairly new kid on the block. But being new has its advantages as it has certain unique features that are not available in the existing ones in the market. Those are:

Real-Time Protection: Prevent malicious software from entering your system.
Alternate modes of scanning: This app consists of different modes of scan like quick scan, deep scan, and custom scan.
Secure Web Browsing: Systweak antivirus includes StopAll Ads extension that will protect adware from entering your system.
Remove Startup item: This application allows users to identify those apps that startup when the computer boots and facilitates removing them if unrequired.
For more information, please read: Systweak Antivirus For PC Review: Finally, Our Computers Can Be Safe & Secure
8. Update The Operating System And Applications

One common misunderstanding observed in many people across the globe is the fact that Updating Software consumes time, internet data and would change certain features that we have become accustomed to. And that is why most people do not pay much attention to or avoid updates. On the other hand, updates are released by software developers to ensure that your application is compatible with your device’s OS and other apps by making important changes related to features, system, and security. If your software is up to date, then it is less vulnerable to hackers.
9. Never Share Personal Information Via Phone, Email, IM, And SMS

One thing about communicating through Phone, Email, Instant Messaging apps, and SMS text messages is that you cannot be sure who is on the other side of the conversation. And that is why you must never share personal information through these channels of communication, lest personal information falls into wrong hands. Even if you are sure and have to provide some info to a relative or friend you trust, you must delete the information from your device and ask him/her to do the same on their device.
Also, take your time to analyze a new email or a text message you received from an unknown sender, and do not click any links or attachments unless sure.
Note: There are many cases of impersonators who run phishing scams online and try to gather personal information through attractive schemes and advertisements which are fake.
10. Be Careful While Disposing Of Old Devices And Postal Labels

The final caution that you must heed while protecting your data is to wipe off personal information on older devices before selling them or disposing of them. A factory reset of the device is a good idea but it is better to use a Hard Drive Wipe Utility Tool to remove the remaining fragments after format or factory reset. Don’t forget to check the older devices for any sort of files and folders stored before handing over the device.
Advanced System Optimizer is one such tool that can wipe your hard drive clean and delete data stored beyond recovery. This app has many modules to optimize your system and one of them is Secure Delete that wipes the free space to avoid critical data recovery and writes zeroes instead.
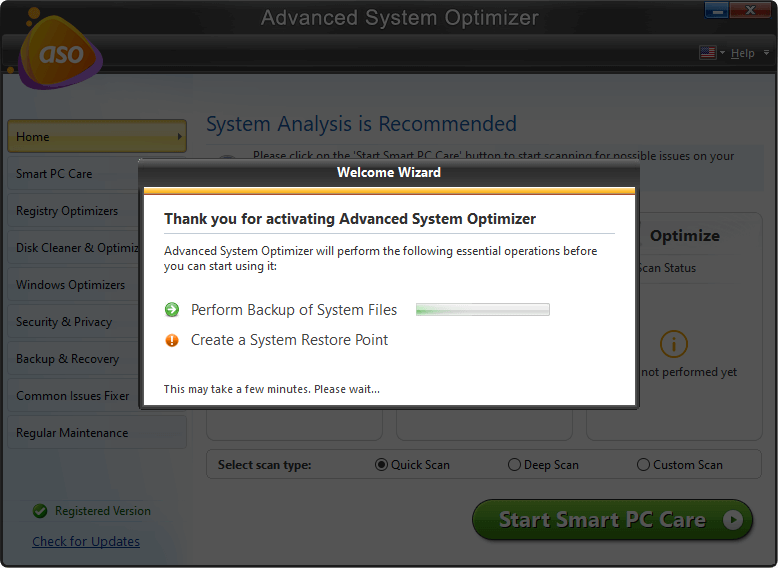
To read more on Advanced System Optimizer, click this link
It is also important to take care while disposing of the postal labels containing your name, address, and phone number on packages and parcels that you receive from someone or by shopping online. You must remove the label from the carton and dispose of it safely so that it does not fall into wrong hands.
Your Thoughts On How To Protect Personal Data
I hope you have understood why it is important to protect your data and different methods on how to do the same. It is important to heed caution and develop certain new habits that will ensure the safety of personal information. If you know of any other method that is not listed here then do mention the same in the comments section below.
Follow us on social media – Facebook, Twitter, and YouTube. For any queries or suggestions, please let us know in the comments section below. We would love to get back to you with a solution. We regularly post tips and tricks, along with answers to common issues related to technology.




 Subscribe Now & Never Miss The Latest Tech Updates!
Subscribe Now & Never Miss The Latest Tech Updates!