VPNs (Virtual Private Networks) have undoubtedly become one of the cornerstones of establishing secure communications over the Internet. But, there’s a lot of confusion when it comes to exploring what a VPN can and cannot do. This confusion had led several individuals to choose a VPN Service that might not be well suited according to their environment, needs, and requirements.
To eliminate all your confusion, we have prepared a thorough glossary of common VPN terminologies. Hope it helps understand the basics of VPN!
Meanwhile, we’ll be talking about the concept of VPN Tunnel, How does it work, and How secure they are? Let’s get into the details!
What Is A VPN Tunnel?
Whenever you connect to the Internet via a Virtual Private Network, you certainly establish a safe connection for information to travel between your device and the Internet. This connection is known as a VPN Tunnel. It is responsible for encrypting every piece of your information, making it simply impossible for anyone to read it (unless one has a specific decryption key).
The entire concept is similar to having a personal courier service instead of public mailing solutions. The only difference is that your courier only delivers and translates every letter into the language, which is only understandable by you. Hence, no matter if any snooper tries to read your message, they will get nothing in return!
So, How Does A VPN Tunnel Work?
Well, whenever your device initiates a connection to the Internet via VPN, your entire network traffic passes through a secure tunnel. Every information sent through this tunnel is split and encapsulated within ‘packets’ (in layers of data). The process works like putting a letter inside an envelope. Hence, no third parties (not even your ISP) can know what’s inside.
As soon as the packet arrives at the final destination (your VPN server) this tunnel gets terminated so that it can access your data. Although the process seems a little complicated, it doesn’t take a lot of time to ensure your entire connection is safer while connected to the web. Now the question arrives, How safe the VPN tunnel is? Well, the answer depends on the protocol you are using.
Must-Read: What Is Double VPN & Should You Use It?
Types Of VPN Tunnel Protocols
Well, the strength of a VPN tunnel depends on the type of tunneling protocol your respective VPN provider uses. Therefore, you must choose a VPN service that relies on the strongest tunneling protocol. Here’s a list of some common VPN Protocols you are likely to encounter.
1. PPTP
Stands for Point to Point Tunneling Protocol, PPTP is one of the oldest versions of protocols, still in use today. Their strength lies in their Speed, you can undoubtedly expect the fastest connection speeds. Although the speed comes at a cost, since the protocol is extremely fast, it certainly lacks the level of data encryption, as compared to current market standards.
This means it becomes easy for hackers to crack the encryption easily provided by this VPN protocol. Hence, if you need better and stronger encryption, then you need to choose another protocol.
Pros
- Fastest protocol ever built.
- Easy to set up.
Cons
- Easily hackable.
- Outdated protocol available.
- Not a suitable choice for maintaining good encryption.
| Do We Recommend? Not Recommended |
2. SSTP
Also known as Secure Socket Tunneling Protocol, SSTP is better known in the market for its ability to transport Internet data via the Secure Sockets Layer of SSL. The protocol is natively supported by Windows, making it super easy for Windows users to set up the protocol without any hassles.
SSTP is known for providing decent negotiation, encryption, and traffic checking. It is a safe VPN tunnel protocol and doesn’t use any fixed ports. Hence, it becomes easy for SSTP to bypass firewalls.
Pros
- Ability to bypass firewalls.
- Arrives with high-end encryption techniques.
- Easy to set up & use on Windows.
Cons
- Difficult to set up on other OS than Windows.
- Never been audited.
- Code is unavailable for VPN developers.
| Do We Recommend? Decent VPN tunnel protocol, but not recommended. |
Must-Read: 5 Unexpected Ways To Save Money With VPN That Will Blow Your Mind!
3. L2TP/IPSec
Stands for Layer 2 Tunneling Protocol used in conjunction with Internet Protocol Security, L2TP/IPSec is certainly a more secure tunneling protocol than PP2P. To be honest, L2TP encapsulates the data, but it gets adequately encrypted when it gets wrapped with IPSec protocol again.
When it’s done, a two-layer of encryption is built to safeguard the confidentiality of the data packets transmitted through the VPN tunnel. L2TP/IPSec offers AES-256-bit encryption, which is one of the most advanced standards of encryption available currently.
Pros
- Better protocol than PPTP, in terms of security.
- Provides fast connections.
Cons
- Certainly outdated.
- Doesn’t encrypt itself.
- Not a suitable choice against bypassing firewalls.
| Do We Recommend? Not recommended, since it uses fixed ports and struggles to bypass firewalls. |
You Might Want To Read: What is VPN Split Tunneling? How Does it Work?
4. IKEv2
Better known as Internet Key Exchange version 2, IKEv2 is a common VPN tunneling protocol that provides a seamless and safe key exchange session. Similar to L2TP, it usually gets paired with IPSec for better encryption and authenticity.
Unlike other protocols mentioned here, IKEv2 is good at re-establishing the VPN tunnel, even if there’s a temporary connection loss. IK3v2 is good at switching the connections across network types (from WIFI to Mobile Data) as per the environment and needs.
Pros
- Fast VPN protocol.
- Mobile-friendly.
- Comes with strong network switching capabilities.
- Has great support for native & third-party clients.
Cons
- Speed depends on the distance between the device & server.
| Do We Recommend? Yes, a great recommendation, specifically for mobile users. |
5. Shadowsocks
Another prominent entry in the list of effective VPN Tunneling Protocols includes Shadowsocks. It is a free and open-source protocol, mainly used by Chinese people to bypass the Great Firewall of China. It is certainly the best choice for unblocking censorships.
It is a useful choice if you wish for the fastest connectivity, want to cover your browser, only and live in a country like China, where there are enormous kinds of surfing restrictions.
Pros
- Good choice for bypassing censorships.
- Receives constant developments.
- Relatively fast.
Cons
- Only suitable for bypassing censorships.
- Only helps in hiding & encrypting browser traffic.
| Do We Recommend? Partially, if you are not living in a restricted country, you should switch to IKEv2, Wireguard, or OpenVPN protocol, which is discussed below! |
Must-Read: Best Paid and Free VPNs for Netflix That Works 2021
6. WireGuard
With 4,000 lines of code, WireGuard is an excellent VPN Tunneling protocol that makes it easier to audit and harder to find flaws to exploit. It uses a blend of the latest encryption techniques, including (Noise protocol framework, Poly1305, ChaCha20, Curve25519, BLAKE2s, SipHash24, HKDF, and more) to provide users with secure established connections via VPN.
Since WireGuard utilizes state-of-the-art cryptography, it aims to be a faster, simpler, leaner, and more useful VPN Tunneling protocol than IPSec.
Pros
- Less susceptible to security vulnerabilities.
- Easier to manage and audit.
- Uses high-speed cryptographic primitives.
- Open-source & free.
- User-friendly & offers stable connectivity.
Cons
- Relatively new protocol in the market.
| Do We Recommend? Yes, highly recommended VPN Tunneling Protocol choice. |
7. OpenVPN
Considered one of the safest and widely available options for VPNs, OpenVPN as the name entails gets constantly developed and improved by security professionals for best results. The VPN Protocol is a highly reliable, safest, fastest choice among the majority of the options mentioned here.
It works seamlessly well for long-distance connections, be it on mobile devices or desktop operating systems. Similar to L2TP/IPSec it uses the AES-256-bit encryption model to protect data packets. If you are looking forward to a VPN service that comes with OpenVPN protocol, then you can use Systweak VPN. Click here, to know better about Systweak VPN!
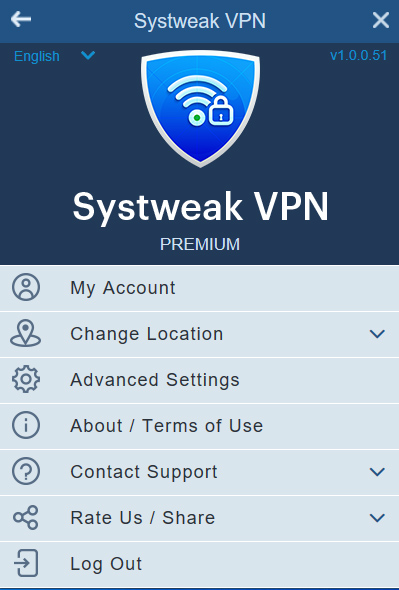
Download Systweak VPN Now
Must-Read: Systweak VPN VS NordVPN Vs PureVPN – Which is the Best VPN for Windows
Pros
- Configurable on Windows, Mac, Android, and IOS.
- Provides strong security & privacy.
- Uses high-end encryption techniques.
- Good authentication & verification.
Cons
- Can be hard to set up, if done manually.
| Do We Recommend? Yes, a highly recommended choice for all types of OS users. |
Protecting Your Digital Privacy
Well, the key to VPN Tunneling is to use a reliable VPN Provider. If you wish for the fastest speeds, you can go with PPTP. If security is concerned, choose L2TP/IPSec, but you might struggle with firewalls, given its fixed ports. If both security and the ability to bypass firewalls is concerned, then you should rely on OpenVPN. It is currently the best VPN Tunneling Protocol available if you wish to keep your Internet data secure.
A good VPN offers you at least four types of Tunneling protocols when going online. We’ve accumulated the list of Best VPN Services available in the market to help you get started on protecting your online activities and data.



 Subscribe Now & Never Miss The Latest Tech Updates!
Subscribe Now & Never Miss The Latest Tech Updates!