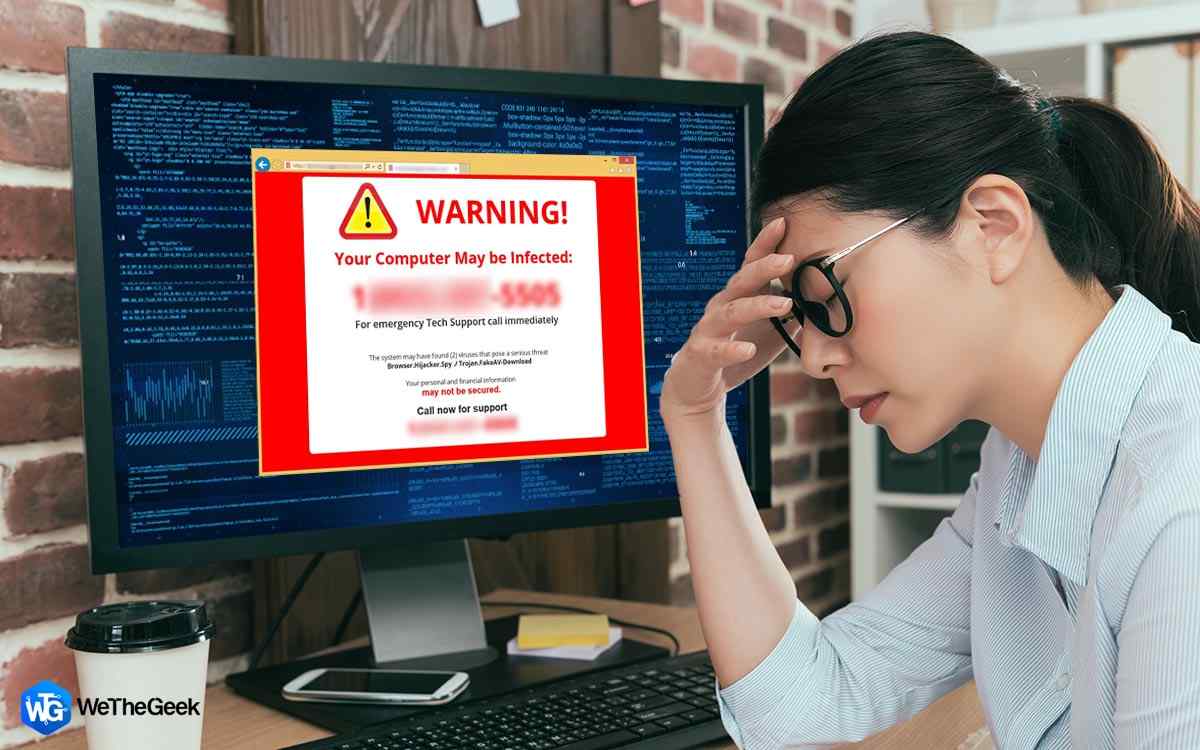
The word “scareware” refers to any advertisement or message that attempts to terrify you into downloading or purchasing needless software. It employs a technique that seeks to shock and worry you and is a type of social engineering. When scareware is at its worst, it can put you in danger of identity theft and credit card fraud. Cybercriminals may even keep the contents of your hard drive hostage until you pay a ransom.
Ransomware is the term for the program employed in this instance. Although scareware can be used to spread ransomware, the two have different objectives. Scareware seeks to offer ineffective, phony utilities that download harmful malware. Data belonging to a user is held hostage by ransomware until a ransom is paid.
How Is Scareware Recognised?

Following an alert, you could fear your computer being infected with malware. Here are some typical symptoms to watch out for:
Several pop-up windows: Scareware can be identified by persistent browser pop-ups that warn of critical security vulnerabilities.
Performance on your machine is deteriorating: Your device may become sluggish, crash, or freeze due to malware.
Randomly appearing new features and programs: You discover toolbars or desktop icons that you didn’t add.
An inability to access files or programs: Users, once infected, are not able to use their apps or files. Instead, unexpected error messages show up.
Your preferences have changed: Your default browser and even your background have changed without your intervention.
You made an ad click: After clicking an ad, if you observe any of those above, you may have been the victim of malicious advertising. The advertisement you clicked on might have contained dangerous program-downloading malware.
How Can Scareware Assaults Be Stopped?

The ideal scenario is never to acquire scareware in the first place because prevention is always preferable to treatment. Follow these recommendations to help stop scareware assaults.
Utilize all available network and cybersecurity tools: Your first line of protection against cyberattacks, including scareware, is to use tools like an antivirus program, firewalls, ad blockers, and a VPN.
Use reliable antivirus programs: Your computer’s malware will be quickly quarantined and removed by antivirus software from a reputable source.
Never click on any virus alerts: Don’t click the “download” button on a pop-up too quickly. Instead, use the Task Manager on your computer to shut down your browser.
Make pop-up blockers active: If pop-ups are avoided, your screen won’t fill up with adverts for phony security programs. From your browser’s settings page, disable pop-up windows.
Update your browser frequently: Ensuring your browser is updated with the most recent security patch helps defend against scareware pop-ups. Think about allowing automatic upgrades.
Check out new software before purchasing it: Do your research before giving out a credit card or personal information to a business that sounds sketchy. You can differentiate between real and bogus software by performing a fast Google search.
Check your device for suspicious activity and attack indicators (IOA): After using an antivirus to remove malware successfully, keep an eye on your device for any unusual activities.
For The Best Results Worldwide, Use Systweak VPN

Users get access to more than 4500 servers spread across 200 cities and 53 countries thanks to the Systweak VPN. In 200 locations across 53 different countries, you can hide your IP address and location. Considering the advantages below, you can determine why Systweak VPN is the ideal choice.
It Aids People in Avoiding Geographical Restrictions
Now, while traveling, you may access all geographically limited information in one location. To view the content, you must connect to the nation’s server.
Genuine encrypting
To secure your privacy, Systweak VPN provides military-grade AES 256-bit encryption. Without access, the hackers are already able to evaluate the data
Activate “Kill” mode
If the VPN server encounters an issue, your internet connection will be quickly stopped, ensuring that none of your data is ever exposed.
Cover up the IP address
If your IP address or location is found, don’t be concerned. To change your IP address, choose one of the safe Tunnel servers.
The Final Word: What Is Scareware And How to Protect Yourself From It?
Pop-ups warn you your device may have a virus or harmful files overwhelms your screen. They keep popping up and urge you to delete them by clicking a button on the pop-up. These strategies rely on social engineering to scare you into purchasing or downloading software. Real antivirus companies won’t intimidate you into taking action. The likelihood that the alerts are scareware increases with their persistence and drama.
Follow us on social media – Facebook, Instagram, and YouTube. Please contact us with any questions or ideas. We would be delighted to provide you with a resolution. We frequently publish advice, solutions, and guidance for common technological problems.