The analysts at Kaspersky concluded that the Andariel group is prepared to target any company rather than concentrate on one industry. In June, the US Cybersecurity and Infrastructure Security Agency (CISA) announced that the US healthcare industry is the primary target of the Maui ransomware, which targets businesses and governmental entities. However, in addition to multiple victims in India, Vietnam, and Russia, at least one attack on a company in Japan.
How Does The Andariel Group Attack – Modus Operandi?

The well-known spyware DTrack is the primary weapon the Andariel organization uses. It gathers victim data and transmits it to a remote host. DTrack gathers browser history and saves it to a different file, among other things. The variant used in Andariel assaults can keep the collected data on a remote host within the victim’s network and send it through HTTP to the hackers’ server.

Maui ransomware is used when attackers discover important data. On targeted hosts, it is often discovered 10 hours after the DTrack virus is activated. The operators manually operate the ransomware and choose which data to encrypt.
3Proxy appears to be another method the attackers are utilizing. Because of its small size, attackers are probably interested in using this trustworthy, free, cross-platform proxy server. To sustain remote access to a compromised computer, employ this tool.
How Does Malware From Andariel Spread?
Hackers use the unpatched versions of open-source web services. In one instance, the attackers used an unidentified exploit to run a Powershell script from a remote server after downloading the malware through an HFS (HTTP file server). In a different instance, they successfully took control of a WebLogic server by exploiting the CVE-2017-10271 flaw, which finally let them execute a script.
How Can I Keep Secure?
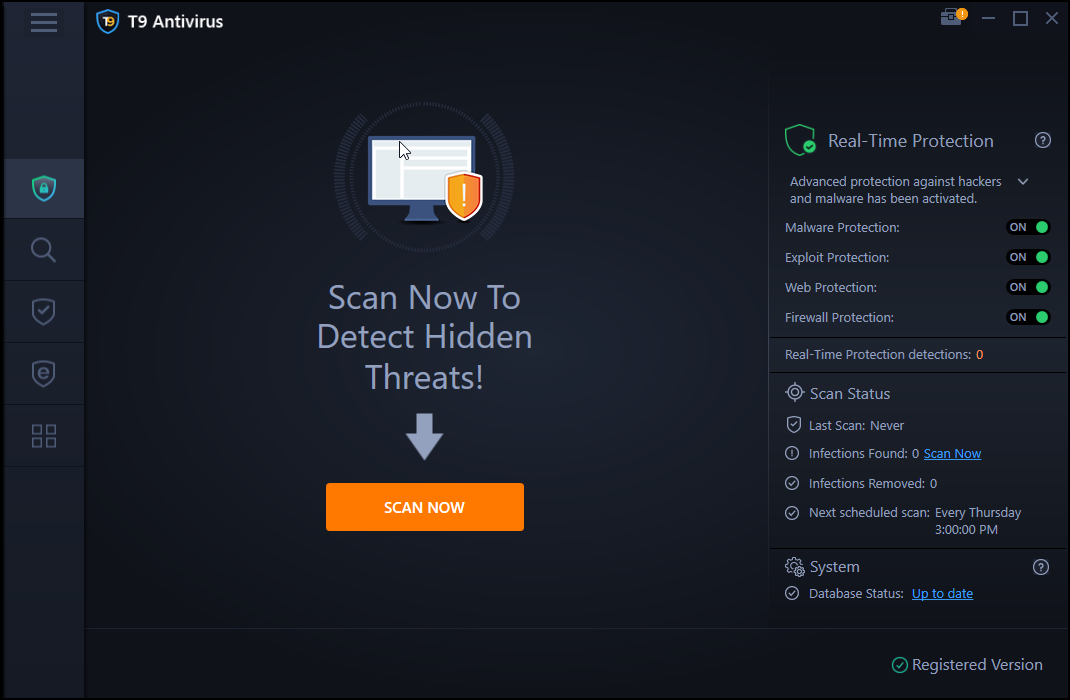
There is no exact solution to Andariel attacks, but one can safeguard against the malware tools they use by using a real-time antivirus. One of the best antivirus tools in this category is the T9 antivirus which received iVB100 certification two years ago and still maintains it. The following are a few benefits of utilizing this software:
Malware Protection
Threats that T9 antivirus defends against include infections, zero-day threats, malware, Trojans, PUPs, adware, and more.
Instantaneous Security
Real-time security identifies and stops malware before it can infect your machine. Security lapses, identity theft, and other threats can all be prevented in this way.
Eliminate startup applications
By quickly identifying and removing unnecessary startup items, you may avoid being taken advantage of by startup programs that are running in the background and endangering the security of your computer and your data.
Prevention of Exploits
Protection against malware infections brought on by security holes is provided by the trustworthy T9 Antivirus Exploit Protection module.
Virus Definitions Updated
Antivirus software must be regularly updated to recognize and get rid of new malware threats as they emerge and hackers refine their techniques. By routinely installing the most recent database definition updates, T9 Antivirus guards you against the most recent threats.
Defend yourself against the most modern and contemporary dangers
One of the major security issues in the networked society of today is the potential for sophisticated assaults. The best method to reduce these hazards is to use a cutting-edge program like T9 Antivirus and malware protection software, which provides real-time security and many defenses. Before data is compromised, security technology recognizes dangers and successfully combats them.
The Final Word On What Are Andariel Attacks And How To Protect Your PC
With its cyber operations, Andariel, thought to be a subgroup of the Lazarus APT group, is wreaking havoc. Malicious hackers target businesses worldwide with DTrack spyware and Maui ransomware. As is customary for Lazarus, the organization demands a ransom in this attack to obtain a financial advantage.
Follow us on social media – Facebook, Instagram, and YouTube. Please contact us with any questions or ideas. We would be delighted to provide you with a resolution. We frequently publish advice, solutions, and guidance for common technological problems.



 Subscribe Now & Never Miss The Latest Tech Updates!
Subscribe Now & Never Miss The Latest Tech Updates!