Phishing is a type of fraudulent activity where threat actors contact their victims by tempting emails, text messages, or by phone calls while impersonating them as a legitimate entity. The victim then responds to the message and follows the instructions provided thinking that these actions would benefit him/her but it results on the contrary. This type of spam is carried out on many innocent people at once and a few are trapped.
| Phishing is similar to Fishing where a fisherman throws a net in the water and a few fish are trapped. |
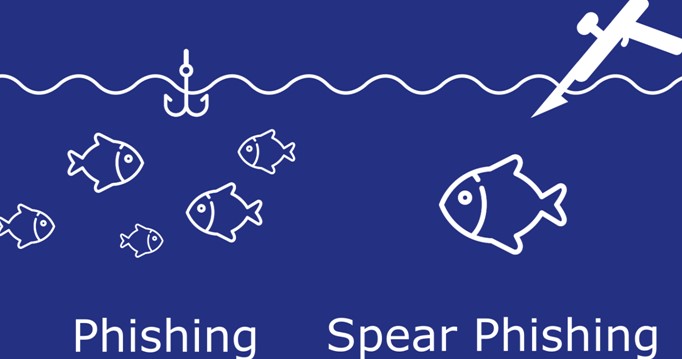
Spear Phishing is a type of Phishing activity that targets specific individuals and organizations. Malicious Actors use Social Engineering techniques and disguise themselves as legitimate entities while sending malicious emails with the corrupted files or links embedded in them. The personalized nature of the email convinces the victim that the email received from cybercriminals is indeed from a genuine source and they follow the instructions within.
| Spear Phishing is similar to Harpooning where one large fish like a Whale or Shark is targeted only. |
Q: How do threat actors get personalized information about individuals or organizations?
A: Read on….
Special Features That Distinguish Spear Phishing From Other MalPractices

- Cyber Criminals target important officials of an organization like the CEO, CFO, VP, etc to get access to valuable data that has limited access. This process within Spear Phishing is also known as Whaling.
- Careful research is carried out by threat actors using LinkedIn and Social Media to find out whom to target and attack by sending personalized messages.
- The data accessed is then used to imitate the tone and requirements of the company and initiate false requests.
- Fake Emails are sent using apps offering temporary email services.
- Symantec’s Internet Security Threat Report 2019 stated that most of the hacker groups (65%) used Spear Phishing as their technique.
Q: How do malicious actors know which emails would individual access?
A: Read on….
Tips On How To Prevent Spear Phishing Attacks

- Do not open emails or download attachments from unknown senders to protect from spear phishing
- Analyze emails and look for spelling and grammar mistakes. If present, then it is probably a scam email.
- Ensure you use a difficult password and prevent spear phishing
- Enable Two-factor authentication at all times.
- Never provide information to outsiders unless you are 100% sure of to protect from spear phishing
- Never display your official email address on a public forum and use a general email or fill out a form instead.
- Use a real-time antivirus and ensure it is updated regularly
- Use a Virtual Private Network to access data from the internet to protect from spear phishing
- Learn more about Phishing and share this information with your colleagues and prevent spear phishing
Q: How do cybercriminals know the inside-out of a company?
A: Read on….
Virtual Private Network Helps To Protect Information About Online Activities
Q: Here is the answer –
A: Hackers and other threat actors gain access and snoop over the network and try to utilize all the bits of information they can grab. The best possible solution is to use a VPN that would ensure that your data is encrypted before being transmitted over the network.
A virtual private network or VPN for short helps users to create a personal and secured network. This ensures that all data and information that leaves your PC is encrypted and travels through a secured VPN tunnel. It is decrypted only when it reaches its intended destination and vice versa. This ensures that the threat actors do not get any data at all that would make sense or can be utilized to generate a strategy of fake emails. There are many VPN services available and it is strongly recommended never to opt for free software. Hence we recommend using Systweak VPN which is an amazing software that can protect your data and traffic.
The Best VPN for PC – Systweak VPN

Systweak VPN service offers 500+ servers, in 200+ locations and 53 countries around the world with a monthly subscription for just under $10 with cheaper monthly and yearly rates. This efficient VPN service has been regarded as the best choice by Industry Experts and is trustworthy as it does not collect any data.
Features:
- Access Global Content
- IKev2 Secure tunnel
- AES 256-bit military-grade encryption services
- Avoids ISP throttling
- Kill Switch to assure no data leaks.
The Final Word On What Is Spear Phishing and How to Protect Yourself from it?
Spear Phishing is a targeted activity and if you are important enough for the company, then you can become the next target. Constant Vigilance is the Mantra against Phishing and Antivirus & VPN are the best tools that can aid to protect you from any sort of malicious attacks. Once the channel of communication To & From your network is encrypted by Systweak VPN, the data is safe and secure and cannot be encrypted even if the threat actors manage to get bits and pieces. Follow us on social media – Facebook, Instagram and YouTube.



 Subscribe Now & Never Miss The Latest Tech Updates!
Subscribe Now & Never Miss The Latest Tech Updates!