A brute force assault is one of the most basic and poor hacking techniques. The assumption behind such an attack is that if you guess a password an endless number of times, you will ultimately be correct. By attempting to guess the username/email and password, the attacker hopes to acquire forced access to a user account. The goal is usually to exploit the compromised account to launch a large-scale attack, steal important data, take down the system, or do all three. It takes little ingenuity or knowledge to write code that executes this type of attack, and there are even readily available automated systems that submit thousands of password attempts each second. This guide helps readers on how to prevent brute force attacks on your PC.
How to Prevent Brute Force Attacks
A robust password policy is the most evident. Strong passwords should be enforced by every web application or public server. Standard user accounts, for example, must contain a combination of eight characters consisting of numbers, uppercase and lowercase alphabets, and special characters. Furthermore, servers should mandate password updates regularly.
There are other methods that we need to follow in addition to maintaining strong and unique passwords Here is a list of different methods:
1. Set An Account Lock Policy After 3 Failed Attempts

Implementing an account lockout after a series of failed login attempts is futile since it puts your server vulnerable to denial-of-service assaults. This procedure, however, becomes considerably more effective when performed with successive delays.
After a certain number of unsuccessful login attempts, account lockouts with progressive delays lock an account for a specific amount of time. Automated brute force assault methods will become less useful as a result. Admins will also save time by not having to unlock hundreds of accounts every few minutes.
2. Using SSH, Alter settings to make the root user inaccessible
Attempts to brute force SSH passwords on a server’s root user are common. By modifying the sshd_config file, ensure that the root user is not accessible through SSH. Set the parameters for ‘DenyUsers root’ and ‘PermitRootLogin no’. This is regarded as the key step on how to prevent SSH brute force attacks.
3. Make a change to the Default Port

The default port 22 is used in the majority of automated SSH attacks. As a result, running sshd on a separate port might be a good strategy to avoid brute force attacks. Edit the port line in your sshd_config file to change to a non-standard port. This step is recommended by ethical hackers as a Must-Do method on how to prevent SSH brute force attacks.
4. Make use of CAPTCHA

On the internet, we’ve all become accustomed to seeing a CAPTCHA. Nobody enjoys attempting to decipher something that appears like it was scrawled by a two-year-old, yet solutions like CAPTCHA make automated bots useless. When working on how to stop brute force attacks, the old-fashioned Captcha can still help you deter the hackers.
Even though hackers have started employing optical character recognition software to get around this safety measure, the simple requirement to enter a word or the number of cats on a generated image is quite effective against bots.
5. Restrict Logins to a Specific IP Address or Range of IP Addresses

If you only grant access from a specific IP address or range, brute force attackers will have to work extra hard to get past that barrier and acquire access.
It’s like erecting a security fence around your most sensitive information, and anyone who doesn’t come from the correct IP address is denied access. You can do this by assigning a static IP address to a remote access port. You can use a VPN instead of a static IP address if you don’t have one.
6. Make use of two-factor authentication (2FA)

Many people consider two-factor authentication to be the first line of defense against brute force attacks. This is a highly recommended step under how to stop brute force attacks and the risk of a data breach is considerably reduced when such a solution is implemented.
The beauty of 2FA is that a password alone isn’t sufficient. An attacker would need access to your smartphone or email client even if they cracked the password. Some determined attackers may try to breach that barrier, but the majority will turn around and go for a less difficult victim.
7. Keep an eye on your server logs
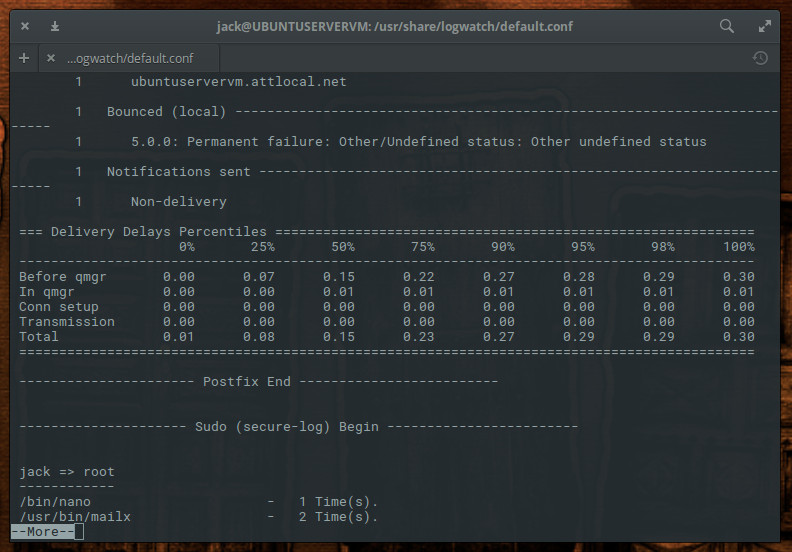
Make careful to thoroughly examine your log files. Log files are critical for system upkeep, as administrators are well aware. Log management software, such as Logwatch, can let you run daily audits and generate daily reports automatically.
Bonus: Systweak Antivirus, An App to detect real-time malware

The above methods on how to stop brute force attacks are recommended by experts and have been implemented by many. But in cases where an infiltrator manages to get malware into your system, then you would need a powerful real-time antivirus to identify it with immediate effect and eliminate the threat. For this very purpose, I suggest using Systweak Antivirus.
Systweak Antivirus protects your computer from all forms of malicious assaults and provides real-time protection. It also includes the StopAllAds browser plugin, which filters unwanted advertisements and safeguards the computer by preventing malware and other types of malicious software from being downloaded or accessed. Systweak Antivirus guards your computer against exploits around the clock, 365 days a year. It boosts the computer’s present performance by acting as a one-stop-shop for all security needs.
Security in real-time. One of the few antivirus programs that can detect potential threats/apps based on how they behave on your computer is Systweak Antivirus.
It’s quite easy to use. This program offers a simple user interface that everyone in your family may use.
Light-Weight. Software that uses the fewest system resources is considered the best because it will not block your CPU resources.
Secure Web Browsing. This app allows browsing the internet using an ad blocker plugin to stop advertising while surfing the internet.
Remove unwanted items from the computer’s startup menu. Users can turn off starting components that make the computer take longer to boot.
The Final Word On How To Prevent Brute Force Attacks With 7 Easy Tactics
If you are looking at How To Prevent Brute Force Attacks on your PC, then the above-listed methods can help attain a certain level of security and safeguard your system. Determinant hackers can still get past these various methods and you will have to keep your system updated at all times. As far as malware is concerned, Systweak Antivirus plays a vital role in removing all the hacker-friendly files from your system.
Follow us on social media – Facebook, Instagram, and YouTube. For any queries or suggestions, please let us know in the comments section below. We would love to get back to you with a solution. We regularly post tips and tricks, along with answers to common issues related to technology.
FAQs –
What is the prevention for brute force attacks?
The most obvious technique to prevent brute-force assaults is to freeze accounts after a certain number of failed password attempts. Account lockouts can last a set amount of time, such as one hour, or they can last until an administrator manually unlocks the accounts.
What are the best defenses against a brute force login attack?
Two-Factor Authentication is another efficient defense to prevent Brute Force Login Attacks because it requires more than just a password. Even if the malicious actors obtained the password, they would still require access to your smartphone or email client. Some committed attackers may attempt to get through that barrier, but the majority will turn around and seek out a less challenging victim.
What other features can be put in place to prevent brute force attacks?
Complex Passwords, Captcha, modifying SSH settings, and limiting login from a specific range of IP addresses are a few methods to prevent brute force attacks in addition to two-factor authentication and freezing accounts after certain unsuccessful attempts.



 Subscribe Now & Never Miss The Latest Tech Updates!
Subscribe Now & Never Miss The Latest Tech Updates!