Do you remember last time when you visited your favorite ice cream shop to buy yourself an ice-cream? Now did you think how that shop ended up being your favorite shop? Probably because the shopkeeper has understood your preferences. Your frequent visits have helped him identify you and your identity revealed your interests to him.
What Is Identity?
Identity includes traits that describe you as a person (expressions, qualities, personality and looks). Identity helps people to recognize others and if anyone doesn’t have an identity, he is dead meat for the world.
Identity = Existence
However, Identity is often undermined, especially when it comes to online identity. Relating it to present business trends, what do you think works as a great fuel to businesses? The same fuel that worked for the shopkeeper at the Ice-cream store. You need digital identity to know your customers better.
So, how are these identity solutions going to help business? What is online and digital identity? Read On!
Digital identity or Online identity?
Online Identity is something you create for your online activities such as shopping online, banking, social media etc. Digital Identity is any digitized information of a person (any attribute that can be used to represent him/her).
So, as of now online identity and digital identity can be considered the same in a broader aspect.
The Story of Digital Identity

In 1990’s, the need for replacing poor online registration system produced Microsoft’s Passport (which is also called Identity 1.0). Altogether, it wasn’t a big hit. Later in 2010, Social Login (Identity 2.0) was introduced where you could easily login through your social media profiles. It was well-accepted by many businesses and many online consumers anticipated with organizations. It elevated the status of digital identity.
Result: Many business sites allowed social login.
Now IoT (Identity 3.0) helped our devices to connect with each other. In near future, giants like Google and Apple will invest more on projects related to biometrics and other technologies (e.g.: – touch ID by Apple). Thus, the writing is clear on the wall.
Digital Identity and its authentication methods are evolving.
Why Is It Important For Your Business?
We all want to do well in business. Therefore, to do well, you need customer data that can be arranged through digital identity of a customer.
A digital identity tells you how genuine your customer is and includes attributes like social media data (wiz. first hand data), data gathered from from forums and internet activities etc. Basically, it provides you every data present online that reveals your prospect. It also helps you to differentiate genuine prospects from fake traffic that hits your website.
Your business reaches better heights and user experience skyrockets due to digital identity. Moreover, storing customer preferences would assist you build a solid customer database that will boost your sales. We can put this way- Lose your personalization mojo, lose your customer.
Digital Identity is growing and it supplies you with information such as customer transactions, bill payments, preferences, social media data etc. Moreover, with the introduction of IoT, digital identity will grow rapidly. It will help business to mold its services according to customer preferences. Digital identity has transformed itself into a currency of wide acceptance and its participation remains inevitable. It has become a catalyst for business growth.
Now as you’re familiar with the term digital identity and its capabilities to boost your business, you should learn about different methods to collect digital identity.
Digital identity has evolved a lot, from the primitive email/customer registration service to the latest biometrics mediums. When Internet was accepted as a medium for business, customer registration process came into existence and it was basically designed to acquire customer data. However, the most obvious question that triggered people to imagine about different techniques to create and gather digital identity was- “What type of information does your business require from prospects?”
Hence, they experimented with lengthy and irritating forms but they certainly shooed away customers from websites. This is how they looked like: –
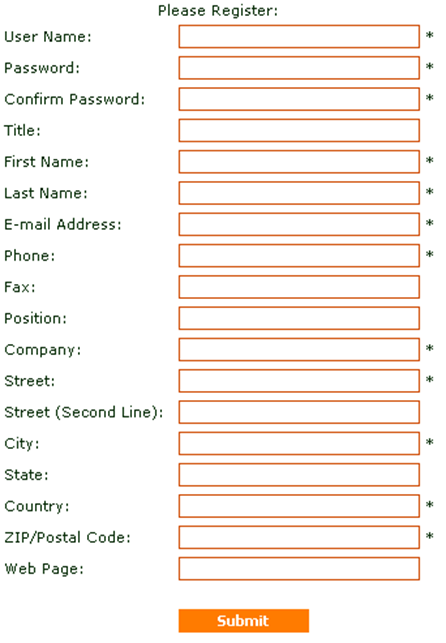
Maximum number of fields were inserted into the form in order to pull out maximum customer data. Unfortunately, they became a canker for customers and ruined customer experience. Thus, the process evolved into following techniques that are still being used for gathering customer data. The list is as follows: –
Designers thought of shrinking registration forms by only including relevant fields. So, email login was introduced.
Email Login
With email login, data associated with the email account is fetched with user concern to create a user persona. It helps to create digital identity of a customer.
How Does It Work?
When the customer adds his/her email address in the form, it sends a link to their inbox. Further, prospect needs to click the link for confirmation and then he/she can avail services on the website. Customer gets automatically logged into the website, next time he/she visits.
Traditional email login seemed monotonous and people hated when they needed to create new accounts for every single website they wanted to utilize. Additionally, they had to remember credentials for all of them. They experienced “password fatigue”. In a survey, it was found out that 86 percent people hated creating new accounts for every single service they benefited. Gradually, websites started losing customers due to the registration process. Hence, social login was introduced.
Social Login
Note: – According to the research by WebHostingBuzz, 77 percent users consider social login as a solution to customer registration fatigue.
Social login took the online business world by storm. It transformed the entire registration process into a game of few clicks. And both customers and organizations loved it.
How Does It Work?
Your customer does not need to create new accounts on your website.
- Your customer logins into your website via social networking site.
- Social Login contacts the server of the respective social networking site for customer authentication.
- The social site authenticates the customer.
- Customer is set to access the website.
Thus, customers saved themselves from the hassle of generating new accounts and then memorizing their passwords.
Phone Or Digit Login
Gradually, the entity email address got replaced with phone number. The technique is called phone or digit login.
With phone login, customers need not to create or remember an extra string of characters.
Also, OTPs (one time passwords) can be used instead of passwords.
How Does It Work?
Your customer accesses the site and logins through a phone number and dedicated OTP or a password as per preference.
Passwordless Login/ One click Login
As per evolution, a new form of customer registration was designed, which is called passwordless login. It was introduced with an aim to eliminate passwords from login. Customers were not required to create a password for the account. An email link called ‘magic link’ would be sent to the customer’s email address.
How Does It Work?
- Customer puts email address while creating account
- Magic link (it includes token embedded within the link) is sent to user to authenticate and authorize customer
- Customer clicks the link (time-bound) and authenticates himself
- Further, he enjoys the website
Progressive Profiling
Although all the techniques simplified registration process, there was no single authentication method that could efficiently content all website requirements without keeping the user experience at stake. Therefore, progressive profiling was introduced to capture user data step by step.
Progressive profiling can help your businesses gather the most essential data from the customer and then gradually collect less important information in consequent interactions. It’s one of the best methods to collect user information without spoiling user experience.

Businesses can integrate secure practices like using the OTP technique, QR codes, RSA token with the regular identity creation methods mentioned above.
Advanced Authentication Methods
Due to continuously evolving cyber-attacks, advanced authentication methods are being developed to prevent hackers from breaching organizational data.
Note: – Though these methods are secure, they need an external device to authenticate users.
Biometrics
Various techniques that is powered by biometrics have been introduced to authenticate and authorize users. They are as follows: –
- Fingerprint: – A Fingerprint scanner is required to scan the unique pattern of fingerprint. It helps businesses authenticate and authorize users/customers to access their services.
- 3D- Face Recognition: – 3D Face recognition scans minute details of the human face like chin, nose measurements, etc. It needs exact measurements areas such as super ciliary arches, chin zone, nose bridge and eye sockets. The technique chooses these areas because they don’t modify with age and time. Therefore, they are dependable. The device contains a light source that helps in recognizing the face in poor light conditions. The near infrared pattern in the 3D face recognition helps recognize every geometric and angle pattern. It maps different angles of the face to confirm the identity.
- Multiple Biometric Authentication: – For enhanced security, organizations can practice multiple biometric authentication. They can add two or more authentication techniques according to the nature of the service. It will take their multiple security to another new level. Generally, such techniques are used by government institutions that manage highly confidential data.
- Mobile Biometric Technology: With mobile biometric technology, the user authenticate himself from anywhere. He doesn’t need to be physically present at the place to verify himself. The authentication device is mobile and can be taken to the user for authentication if necessary.
With these methods, you can not only gather digital identity but also store them securely.
Digital identity can be considered as one of the best additions of the decade. Hope that we are successful in making you understand the real power of Digital Identity. Let us know if you liked our effort in the comments below.


 Subscribe Now & Never Miss The Latest Tech Updates!
Subscribe Now & Never Miss The Latest Tech Updates!