A new Zero-Day exploit has been discovered that is linked to Windows’s MSDT tool. MSDT stands for Microsoft Support Diagnostic Tool, and this exploit allows hackers to infiltrate the targetted PC and run Powershell commands remotely from anywhere. It is known as CVE-2022-30190, and this racker code has been assigned to this vulnerability. We can disable the MSDT key from the Windows Registry, which is the entry point for these malicious attackers.

As explained by researcher Kevin Beaumont, the exploit uses Word’s remote template function to get an HTML file from a distant web server. Subsequently, the code is loaded, and PowerShell instructions are executed via the ms-msdt MSProtocol URI scheme. The exploit was given the name “Follina” since the sample file has the area code 0438, the Follina, Italy area code.
How to Fix Microsoft “Follina” MSDT Windows Zero-Day Vulnerability
So far, until Microsoft releases a security patch and distributes it through its patch Tuesday updates, the only solution to fix this issue is by disabling the MSDT URL Protocol. Here are the steps you can take to protect yourself against the Follina Zero-Day Vulnerability.
Step 1: Press Windows + S on your keyboard to open the Windows Search box and type CMD.
Step 2: Once the search result appears, look for Command Prompt and choose Run as Administrator to run this app in elevated mode.
Step 3: The next step will take a backup of your Windows Registry. Copy and paste the following command in your command prompt, followed by the Enter key.

reg export HKEY_CLASSES_ROOT\ms-msdt <file_path.reg>
Note: The file_path should be replaced by the location where you want to save the Registry backup file. Once the official Microsoft patch for this issue, you can roll back your Registry by using this backup.
Step 4: After the Backup is successfully done, you can copy the following command followed by the Enter key.
reg delete HKEY_CLASSES_ROOT\ms-msdt /f

Step 5: Wait until you get the message “The operation completed successfully” on the Command Prompt window, which indicates that the process is successful.
Step 6: To restore the changes you have carried out, you can import the registry backup taken before executing the command in step 4.
Step 7: Run the following command to reaccess the MSDT URL Protocol.
reg import <file_path.reg>

Bonus Feature: Use Systweak Antivirus To Protect Against Malware
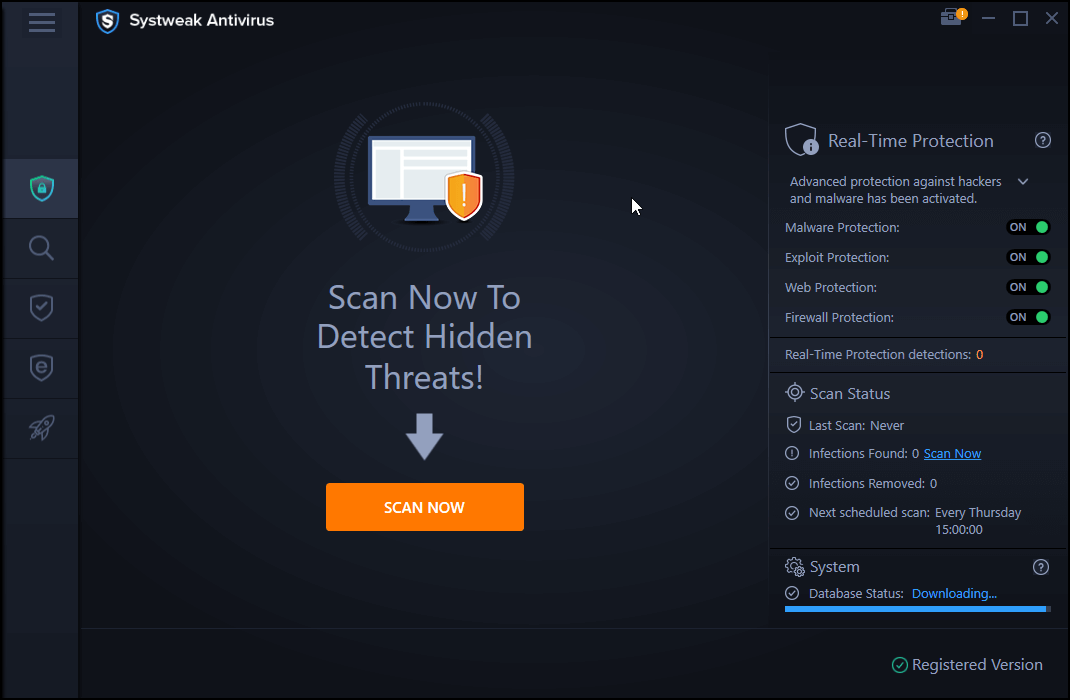
Systweak Antivirus is one of the finest antivirus tools to protect your computer from malicious software like viruses, trojans, worms, spyware, adware, and more. It also contains a module to Stop all ads while browsing the internet. This real-time antivirus offers exploit protection and a separate module to disable the startup items that slow down the boot time of your PC.
Systweak Antivirus keeps you protected against the latest dangers by regularly installing fresh database definition updates. It defends your PC against the most advanced and up-to-date threats. This application is a robust anti-virus application for Windows. With a detection rate of around 99 percent, Systweak Antivirus is one of the most reliable protection software. Systweak Antivirus comes with a 30-day trial version to scan your computer for malware. Furthermore, it consumes relatively low PC resources.
The Final Word On How to Fix Microsoft “Follina” MSDT Windows Zero-Day Vulnerability
I hope the above steps help you fix your PC’s Microsoft “Follina” MSDT Windows Zero-Day vulnerability until a permanent fix arrives. You can always trust Systweak Antivirus on your PC for other malware and viruses that spy on you or harm your computer.
Follow us on social media – Facebook, Instagram, and YouTube. Please let us know of any queries or suggestions in the comments section below. We would love to get back to you with a solution. We regularly post tips and tricks and answers to common issues related to technology.



 Subscribe Now & Never Miss The Latest Tech Updates!
Subscribe Now & Never Miss The Latest Tech Updates!